Why Security Testing Needs to Move Beyond Annual Penetration Tests
Penetration testing has long been a core part of most security programmes. For many organizations, penetration testing follows a familiar model. A test is performed once a year, vulnerabilities are identified, a report is produced and remediation work begins.
For a period of time following the assessment, the organization has a clear view of its security posture.
The problem is that the threat landscape doesn’t wait twelve months for the next penetration test.
New vulnerabilities are disclosed every day. Exploits become available. Attack techniques evolve. Attackers continuously scan the internet looking for vulnerable systems. In fact the National Vulnerability Database recorded over 28,000 new vulnerabilities in 2023 alone, highlighting just how quickly the threat landscape is expanding.
Security testing performed once or twice a year provides useful insight, but ultimately it represents a snapshot in time.
Continuous penetration testing addresses this gap by providing ongoing visibility into vulnerabilities, exploit activity and attack surface changes as environments evolve.
The Problem with Point-in-Time Penetration Test
Traditional penetration testing typically looks like this:
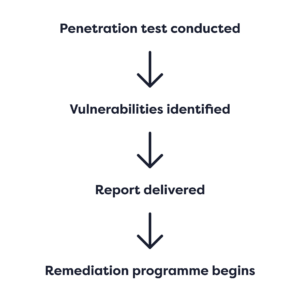
Following the test, organizations have a reasonable understanding of their exposure.
However, risk does not remain static.
Between penetration tests:
- new vulnerabilities may appear
- systems may be exposed to the internet
- new exploits may become available
- attackers may begin targeting specific technologies.
In other words, the environment continues to change while the test results remain fixed in time.
Why Risk Changes Between Tests
Several factors cause security risk to evolve between penetration tests.
New Vulnerabilities Are Discovered
Software vulnerabilities are disclosed continuously across operating systems, applications and infrastructure.
Even well-managed environments can develop new vulnerabilities as systems are updated or new services are deployed.
Exploits Become Available
A vulnerability may initially exist without a reliable exploit.
Once a working exploit becomes available, attackers can automate exploitation and begin scanning for vulnerable systems.
This is often the moment when a vulnerability becomes significantly more dangerous.
Infrastructure and Attack Surfaces Change
Modern environments change frequently.
Applications are deployed, services are exposed to the internet and configurations evolve.
These changes can introduce new attack paths that were not present during previous testing.
What Continuous Penetration Testing Means
Continuous penetration testing moves security testing from a periodic exercise to an ongoing process.
Rather than relying solely on annual penetration tests, organizations maintain continuous visibility into vulnerabilities and attack surface exposure.
At Rootshell, continuous penetration testing combines several key components:
- Manual ethical hacking
- Automated vulnerability discovery
- Attack surface monitoring
- Exploit intelligence
- Automation and remediation workflows
Together, these capabilities provide a much more accurate understanding of security risk as environments and threats evolve.
The Rootshell Continuous Testing Model
Continuous testing at Rootshell begins with manual penetration testing performed by experienced ethical hackers.
This testing identifies vulnerabilities, misconfigurations and potential attack paths across applications, infrastructure and internet-facing systems.
Between testing cycles, the Rootshell Platform performs continuous vulnerability discovery using a combination of proprietary capabilities and carefully selected third-party scanning technologies.
This helps identify new vulnerabilities as environments change.
On top of this discovery layer sits Velma, Rootshell’s exploit intelligence capability.
Velma continuously monitors intelligence sources to identify when vulnerabilities become exploitable or are actively targeted by attackers.
Exploit Intelligence in Continuous Testing
Exploit intelligence adds critical context to vulnerability management. A vulnerability identified during testing may not initially have a working exploit.
Over time, that situation can change.
An exploit may become publicly available through research publications or exploit repositories. When this happens, attackers gain the ability to automate exploitation.
However, there is another important stage.
At Rootshell we distinguish between two key exploit states:
- Exploit Available
- Exploit Active
Exploit Available means a working exploit exists and attackers technically have the capability to use it.
Exploit Active means the exploit is being used in real-world attack campaigns.
This distinction provides an important prioritization signal.
For example:
- Vulnerability identified during penetration test
- Exploit becomes available
- Velma detects that attackers are actively using the exploit
- Priority increases and remediation becomes urgent
By identifying when vulnerabilities move from exploit available to exploit active, security teams can prioritise the vulnerabilities most likely to be used in real attacks.
Automation and Remediation Workflows
Continuous testing is not just about identifying vulnerabilities. It is also about responding quickly when risk changes.
The Rootshell Platform enables organizations to define automation rules and remediation workflows that trigger actions when certain conditions are met.
For example:
- Vulnerability identified
- Exploit detected by Velma
- Risk level automatically increases
- Remediation workflow triggered
This allows organizations to focus remediation efforts on the vulnerabilities that represent the most immediate risk.
Why Continuous Penetration Testing Matters
Attackers do not operate on annual schedules. They continuously scan the internet for vulnerable systems and newly exploitable vulnerabilities.
Security testing must therefore evolve to match this reality.
Continuous penetration testing allows organizations to move beyond point-in-time assessments and maintain an ongoing understanding of their security posture.
By combining manual ethical hacking, vulnerability discovery, exploit intelligence and automated workflows, organizations gain clearer visibility into which vulnerabilities represent genuine risk.
Continuous Testing and the Future of Security Programmes
As environments become more dynamic and the number of vulnerabilities continues to grow, periodic testing alone is no longer sufficient.
Security programmes increasingly require continuous visibility into vulnerabilities, exploit activity and attack surface changes.
Continuous penetration testing provides a framework for maintaining that visibility over time.
By combining human expertise, automated discovery and exploit intelligence, organizations can prioritise security efforts based on how attackers operate.
Frequently Asked Questions
What is continuous penetration testing?
Continuous penetration testing is an ongoing approach to security testing that combines manual testing, automated vulnerability discovery, and exploit intelligence to provide real-time visibility into security risk as environments change.
How is continuous penetration testing different from annual penetration testing?
Annual penetration testing provides a snapshot of security at a single point in time, while continuous penetration testing delivers ongoing visibility into vulnerabilities, exploit activity, and attack surface changes throughout the year.
Why is annual penetration testing no longer enough?
Annual testing cannot keep pace with how quickly vulnerabilities are discovered, exploits are developed, and environments change. This creates gaps where organizations may be exposed to risk between tests.
What are the benefits of continuous penetration testing?
Key benefits include:
Ongoing visibility into security risk
Faster identification of new vulnerabilities
Better prioritization using exploit intelligence
Reduced exposure to actively exploited threats
Is continuous penetration testing suitable for all organizations?
Continuous penetration testing is particularly valuable for organizations with dynamic environments, frequent changes, or large attack surfaces, but it can be adapted to suit businesses of all sizes.
How often should penetration testing be performed?
While traditional penetration testing is often conducted annually, modern security programs benefit from continuous testing to maintain visibility and reduce risk throughout the year.
Does continuous penetration testing replace traditional penetration testing?
No – continuous penetration testing builds on traditional testing by extending it into an ongoing process, combining manual expertise with automated discovery and intelligence.
Can’t find the answer to your question?
You can always Contact Our Team of experts for a chat!