Red Team as a Service
Simulate the entire lifecycle of a real-world cyber-attack. Rootshell Security’s Red Team as a Service fully assesses your organization’s ability to detect and respond to sophisticated attack scenarios.
Trusted by companies of all shapes and sizes
What is a red team assessment in cybersecurity?
A red team assessment is the ultimate way to test your organization’s ability to detect and respond to cyber-attacks. Using the same methods as real-world threat actors, a red team assessment launches a safe but realistic attack simulation to evaluate the resilience of your organization at each stage of the attack lifecycle.
Our in-depth, intelligence-driven red team service puts your security techniques, processes, and personnel to the test. You will gain full visibility of your security strategy’s strengths and weaknesses, amplifying your situational awareness and empowering you to improve your defences. We closely tailor our red team assessments to your organization and offer an ongoing subscription to support you against ever-evolving cyber threats.
Red team services are different from penetration testing services, which aim to identify as many exploitable vulnerabilities as possible.
The benefits of Red Team security testing
Advanced attack resilience
Securely placing your organization in a stronger position to prepare, detect, deter and recover from a real-world attack, should you be targeted.
Evaluate your defences
In the window between manual assessments, our testing platform will continuously test your networks and alert you of any possible security vulnerabilities.
Review effectiveness of incident response mechanisms
Testing will expose and assess internal response mechanisms and ‘actions upon’ in the case of any detection of the attack.
Continuous improvement
The output from any simulated attack can help improve internal business and user awareness, with output able to be utilised in internal training programmes, and where relevant, support compliance requirements.
Testing security procedures & practices
Providing evidence of what policies and procedures failed or indeed protected the organization during the attack lifecycle.
Full range of cutting-edge hacker techniques
Rootshell Security will work with you, professionally and ethically, to determine your organization’s resilience to an attack.
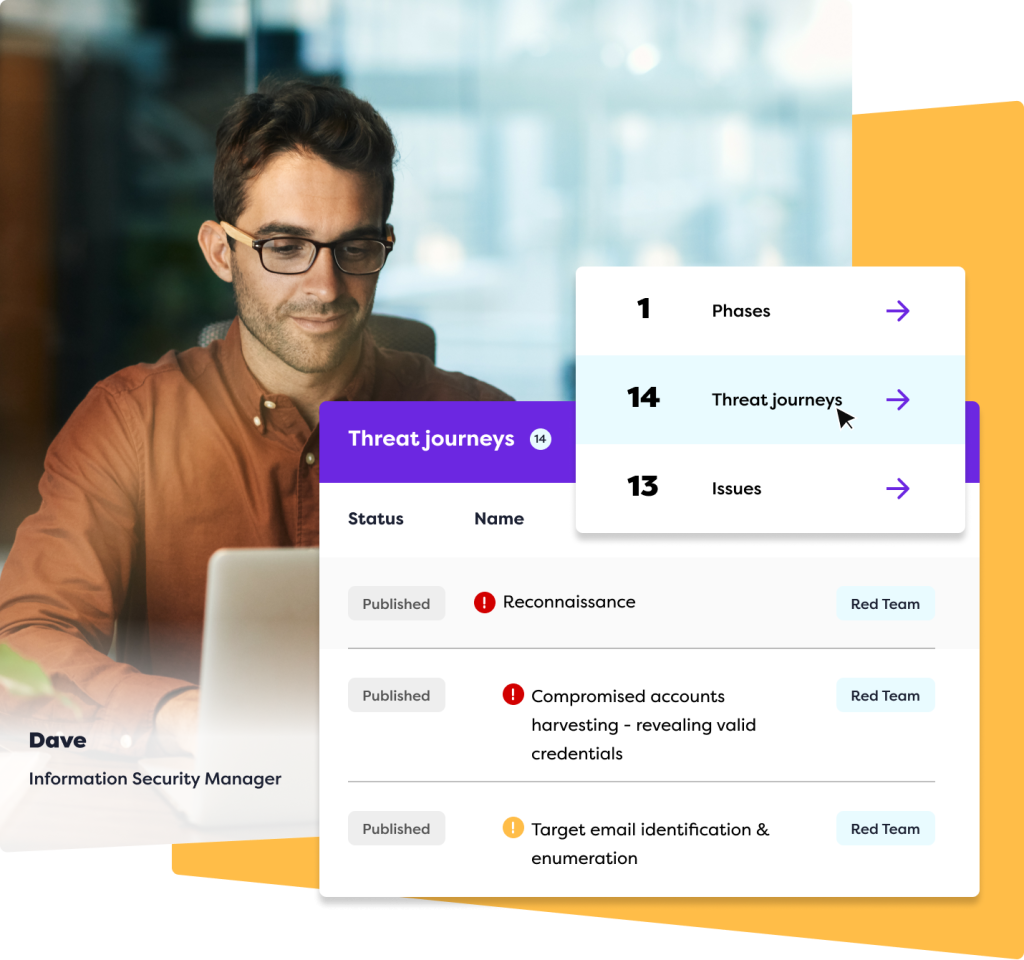
Experience dynamic multimedia red team reporting
Rootshell’s Platform is a vendor-agnostic vulnerability management solution that puts you at the centre of your IT security ecosystem. Consolidate assessment results, accelerate remediation from start to finish, and gain real-time insight into your ever-changing threat landscape.
Recognized industry leader in Red Team As A Service
What is the difference between a penetration test and a red team assessment?
Both penetration tests and red team assessments aim to improve an organization’s security defences by emulating the techniques of a real-world threat actor. But the format and methods of the assessments differ.
A penetration test...
- Is a short term assessment
- Aims to identify and exploit vulnerabilities
- Utilises one attack method
A red team service
- Is a long-term assessment
- Aims to test how well an organization would detect and respond to an attack
- Utilises a broad range of attack methods
What is the purpose of a red team assessment?
Red team services assess how well your organization would perform at each stage of a cyber attack, from reconnaissance to exploitation. You will gain extensive insight into the status of your attack surface and the effectiveness of your security techniques, processes, and personnel.
What you'll test:
- Resilience of your attack surface
- Effectiveness of your threat detection techniques
- Efficiency of your response processes
- Awareness of your personnel
- Gain extensive insight into the status of your attack surface
Plus receive your results and data through The Rootshell Platform .
How are Red team security assessments carried out?
The objective of red team security testing reflects the aim of a real-world threat actor. This could include privilege escalation, data exfiltration, or obtaining the credentials of senior personnel. Our experienced consultants can advise what goal would be most suitable for your organization.
Once we have agreed on a goal for your red team assessment, we carry it out in four steps:
01
Reconnaissance
We employ a range of cyber threat intelligence (CTI) techniques to gather as much information on your organization as possible. This could include open source intelligence (OSINT), financial intelligence (FININT), technical intelligence (TECHINT), and human intelligence (HUMINT). We use this information to identify the targets and methods of our attack
02
Weaponisation and delivery
In this phase, we leverage our intelligence to launch the attack on your organization. Depending on the scope and objectives of your red team assessment, we can execute methods such as email phishing, SMiShing (SMS phishing), physical ingress, or Command and Control activities to exploit vulnerabilities and gain access to your network
03
Exploitation, installation, command & control
Once we have established a foothold, we aim to achieve the agreed objective of your red team assessment. This reveals whether a hacker would be able to attain their end goal. At this stage, we can also simulate different types of threat actors, including a disgruntled employee or an attacker that has gained physical access to your site
04
Continuous reporting
We provide you with clear reports at each phase of your red team security assessment. This gives you full visibility of any vulnerabilities or weaknesses that may exist within your systems or personnel, so you can take action and strengthen your defences
Why choose Rootshell’s Red Team services?
Our vast experience in security testing, threat intelligence, and consultancy for some of the UK’s largest organizations makes us the perfect partner for your red team services.
Subject matter experts
Our in-depth and extensive knowledge of how threat actors operate means we can deliver the best quality red team service possible.
Wide-ranging experience
Our expertise in the full suite of security assessments, including email phishing, physical ingress, and Command and Control activities, means we can test an exhaustive number of attack methods.
Intelligence-driven
As specialists in cyber threat intelligence, we elevate our red team assessment with cutting-edge intelligence-led testing. You will gain a critical awareness of how a threat actor would plan an attack in the first place.
Expert red team consulting
Following your red team assessment, our consultants provide you with clear, detailed, and insightful reports and expert advice so you know exactly how to remediate and reduce risk.
Transform your security posture with Penetration as a Service
Book a demo
Don’t just take our word for it, hear what our customers think
Frequently asked questions about red team assessments
Can’t find the answer to your question?
You can always Contact Our Team of experts for a chat!
How is a red team as a service carried out?
Red team services are carried out in four stages.
Firstly, reconnaissance is carried out to gather as much information about your organization as possible.
Then, we leverage our intelligence to launch a simulated attack on your organization. This could include techniques such as email phishing, physical ingress, or Command and Control techniques, to gain access to your network.
Once we have established a foothold, we aim to achieve the agreed objective of your red team assessment; for example, data exfiltration.
Finally, we provide you with clear reports of how well your organization is performing at each phase of the assessment.
What techniques are used in a red team security assessment?
We utilise a wide range of hacking techniques to carry out red teaming. This includes email phishing, SMiShing (SMS phishing), physical ingress, or Command and Control activities.
What is the difference between a red team and a blue team?
Both red and blue teams are can be considered as types security assessments, but a red team aims to breach an organization, whereas a blue team aims to defend it. The activities of a blue team include network monitoring, risk assessments, and threat detection.
What is the difference between a penetration test and a red team assessment?
Penetration tests are usually short term engagements that focus on exploiting as many vulnerabilities as possible within an organization’s attack vector. Red team assessments are more in depth, long term, and continuous assessments, that utilise a broad range of tactics to infiltrate an organization. The aim of a red team assessment is not only to identify vulnerabilities, but to test an organization’s ability to detect and respond to an attack.
Are they any risks of carrying out a red team assessment
Our highly experienced CREST-certified testers carry out your red team assessment to the highest quality standards, so you can rest assured that no disruption to your organization will be caused.
What is the purpose of a red team services?
Red teaming assesses how your well organization would perform at each stage of a cyber attack. You will gain extensive insight into the status of your attack surface and effectiveness of your security techniques, processes, and personnel.
By conducting a red team assessment you will test the following:
- Resilience of your attack surface
- Effectiveness of your threat detection techniques
- Efficiency of your response processes
- Awareness of your personnel
What are the key benefits of Red team security testing?
Red Team Testing benefits organizations by simulating real-world cyberattacks to uncover vulnerabilities, assess incident response capabilities, and enhance overall security posture. It evaluates people, processes, and technology to identify gaps, prioritize risks, and validate security investments. Additionally, it supports regulatory compliance, fosters a security-first culture, and provides actionable insights for board-level discussions, helping organizations stay ahead of evolving threats.