Managed vulnerability scanning (MVS)
Continuously monitor and maintain your security posture with Rootshell’s managed vulnerability scanning services. This human-led, fully managed service provides year-round visibility of your organization’s vulnerabilities, backed by remediation guidance from our expert team.
Trusted by companies of all shapes and sizes
Understand your assets, risks and threats with managed vulnerability scanning
Continuously monitor and maintain your security posture with Rootshell’s managed vulnerability scanning services. This human-led, fully managed service provides year-round visibility of your organization’s vulnerabilities, backed by remediation guidance from our expert team.
What is Managed Vulnerability Scanning?
Managed Vulnerability scanning is an automated process that uses software to continuously analyze different components of an organization’s network for security vulnerabilities. These scans cover networks, servers, applications, and other digital assets, ensuring continuous detection of vulnerabilities such as outdated software, misconfigurations, and potential entry points for cyberattacks. MVS not only improves your overall security posture but also gives back time to internal teams to focus on business-critical activities.
Once a scan is complete, the scanner provides an exhaustive list of the vulnerabilities identified. It is then up to security teams to manage their results and determine which issues require remediation.
Understanding what vulnerability scanning involves is a useful first step — it enables IT security teams to identify and resolve security issues before they can be exploited by threat actors, and forms the foundation of any effective cybersecurity strategy.

Full Coverage, Year-Round Defense
Using intelligence-driven insights, we can identify if your organization’s infrastructure appears on bad-reputation or “deny-lists” linked to malicious activity. Our managed vulnerability services are designed to be flexible, growing with your organization’s changing requirements. As your goals shift, our service adjusts accordingly, ensuring your network remains resilient against threats. Plus, our MVS can complement your annual penetration testing to provide extra protection.
End-to-End Expert Support
Our experienced security consultants handle every aspect of the process, from initial configuration to detailed reporting. They are always available to provide remediation advice, guiding you on the best steps to maintain a secure environment. Meanwhile, our Security Operation Centre (SOC) analysts meticulously review your vulnerability scan results, reducing false positives and assigning appropriate risk ratings.

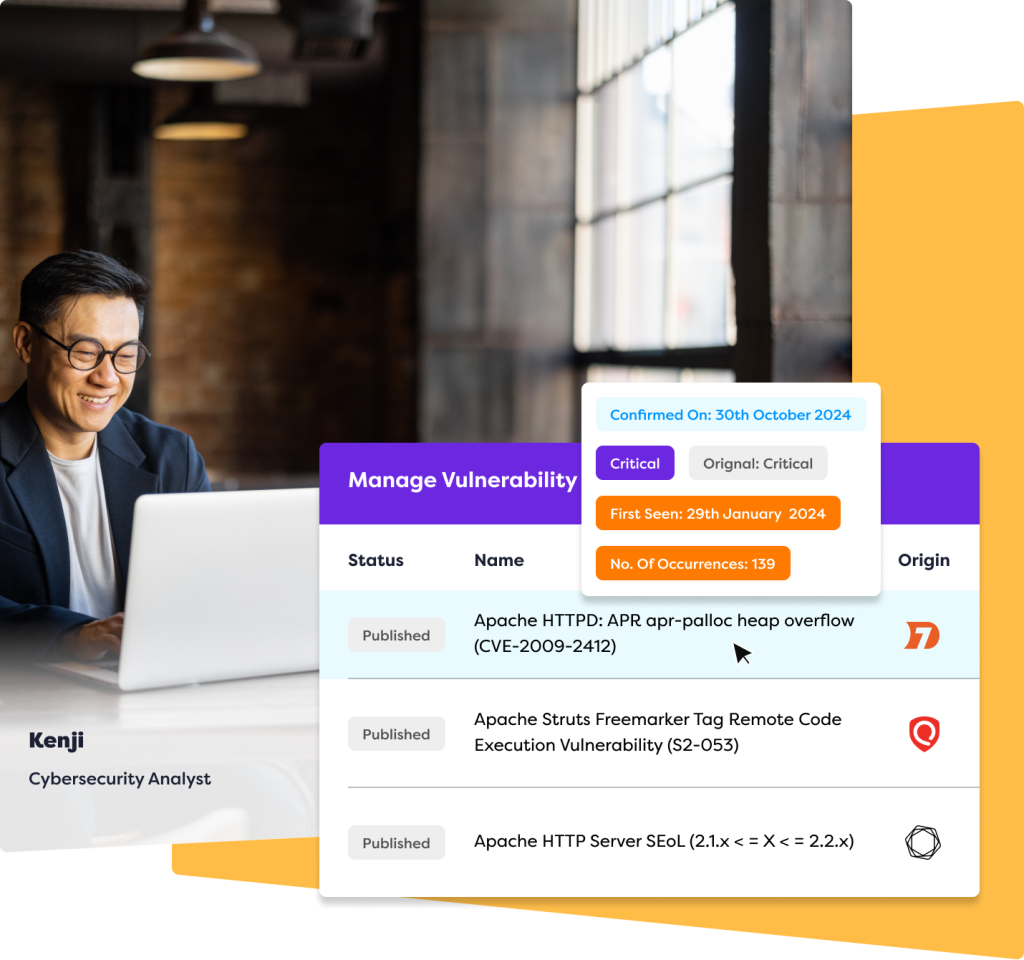
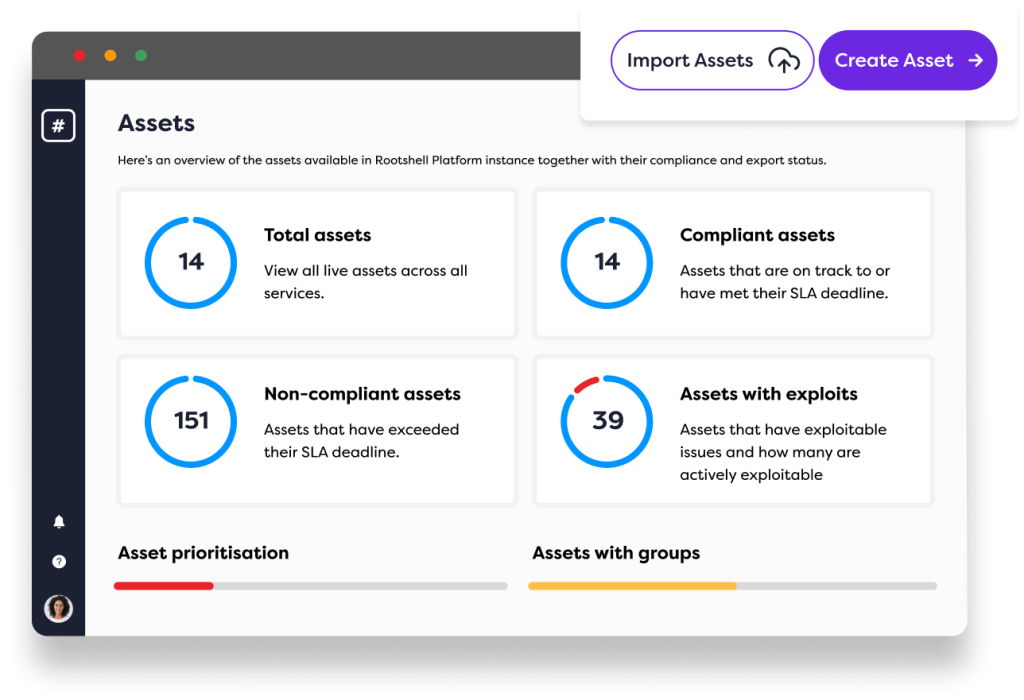
Real-time reporting through The Rootshell Platform
Say goodbye to static spreadsheets! Unlike most cybersecurity providers, we provide flexible reporting through a centralized dashboard, collating and prioritizing all of your penetration testing and attack surface management reports in one place, even if you use other vendors. The Rootshell Platform allows you to see which vulnerabilities need your attention in real-time, speeding up the remediation process.
Hear why the world’s top companies place their trust in us
Managed vulnerability scanning benefits
Managed vulnerability scanning offers significant benefits by providing continuous, expert-driven monitoring of your IT infrastructure. With automated scans and detailed analysis, this service enhances your organization’s security posture, minimizes false positives, and ensures that vulnerabilities are prioritized and remediated effectively.
Regular surveillance
Continuous vulnerability management helps to identify and eliminate security weaknesses. Our managed vulnerability scanning alerts you to issues as soon as they are discovered, providing your organization with round-the-clock protection.
Manual reviews
Our security consultants manually review your vulnerability scans to dismiss errors, false positives, and non-issues, so you only spend time focussing on what’s most important.
Better use of resources
With access to our automation center, our managed vulnerability scanning service frees up your internal team, allowing them to focus on other critical tasks while relying on specialized expertise to keep your defenses strong and up-to-date year-round.
Why choose Rootshell’s managed vulnerability scanning services?
Our highly experienced and dedicated analysts provide the expertise, insight, and advice needed get the most out of your managed vulnerability scanning.
Expertly managed vulnerability scanning
We have the relevant experts on-hand to provide the insight needed to remediate effectively. You will have a dedicated Rootshell Consultant, who holds accreditation by recognized bodies.
Best-in-class tools
When we believe a new or existing product becomes a challenger or market leader, we will deploy it for the benefit of our clients – all at no additional licence cost!
Tailored recommendations
Your organization probably has a vast number of assets, some more important than others. Our security consultants take the time to help you prioritise, ensuring you make the best use of your budget.
Recognized industry leader in penetration testing as a service (PTaaS)
What’s included in Rootshell’s managed vulnerability scanning services?
Your tailored managed vulnerability scanning package includes regular, automated scans across your IT infrastructure, helping to keep your security controls strong and responsive to threats throughout the year. Alongside advanced, real-time reporting, you’ll also benefit from direct access to our cybersecurity specialists, who provide ongoing guidance and expert support.
Our reporting provides you with the data you need to ensure compliance with key standards such as ISO 27001 and Cyber Essentials Plus.
We encourage continuous vulnerability scanning to proactively identify and address potential security risks, keeping your systems protected against threats.
Build your package:
- System misconfiguration
- Unpatched software
- Encryption issues
- Weak credentials
- Injection flaws
- Broken access control
- Broken authentication
- Security misconfiguration
Plus receive your results an data through The Rootshell Platform
Ready to get started?
Discover your needs
Dive into a personalized demo
Seamless onboarding
Frequently asked questions & answers
Can’t find the answer to your question?
You can always Contact Our Team of experts for a chat!
What is the purpose of managed vulnerability scanning?
Managed vulnerability scanning continuously monitors and assesses an organization's IT infrastructure for security weaknesses. By identifying vulnerabilities such as outdated software, misconfigurations, or potential entry points for cyberattacks, it enables proactive remediation before these issues can be exploited. This service helps maintain a strong security posture by providing ongoing protection and reducing the risk of breaches.
Vulnerability scanning vs penetration testing - what’s the difference?
Vulnerability scanning and penetration testing are both essential security practices, but they serve different purposes. Vulnerability scanning is an automated process that identifies potential security weaknesses in your systems by scanning networks, applications, and other digital assets.
Penetration testing is where security professionals simulate real-world attacks to exploit identified vulnerabilities. Penetration testing not only identifies vulnerabilities but also tests the effectiveness of existing defenses.
How do you ensure my vulnerability management is compliant?
To ensure your vulnerability management is compliant, our managed vulnerability scanning service follows industry standards and regulatory requirements relevant to your organization, such as the Payment Card Industry Data Security Standard (PCI DSS), GDPR, HIPAA, and others. Additionally, our service adapts to changes in compliance requirements, ensuring that your vulnerability management remains up-to-date and aligned with legal and industry obligations.
What are the most common ways to manage vulnerabilities?
The most common ways to manage vulnerabilities include regular vulnerability scanning to identify potential issues, patch management to update and fix software vulnerabilities, configuration management to ensure systems are securely configured, and implementing access controls to limit exposure. Additionally, penetration testing helps validate the effectiveness of your security measures, while ongoing monitoring and expert remediation support ensure that vulnerabilities are promptly addressed as they arise.
What assets can be scanned?
Managed vulnerability scanning can cover a wide range of assets, including:
- External vulnerability scanning and internal networks
- Servers and endpoints
- Web applications
- Cloud environments
- Firewalls and network devices
The exact scope depends on your infrastructure and security requirements.
How often should vulnerability scans be performed?
Most organizations run scans monthly or quarterly, with additional scans after major updates, deployments, or configuration changes. Highly regulated industries or high-risk environments may require more frequent scanning to maintain compliance and reduce exposure.
Will vulnerability scanning disrupt my systems?
No. Managed vulnerability scans are designed to be non-intrusive and should not affect system availability or performance. Providers configure scans carefully to avoid disruption, particularly in production environments.