- The Vulnerability Management Cycle is a useful framework for guiding IT security teams’ remediation processes, from discovery to validation.
- Organizations should optimize their vulnerability management cycles to ensure issues are being addressed as fast and efficiently as possible.
- Vulnerability Lifecycle Management Systems like The Rootshell Platform help teams by streamlining workflows, integrating with Cyber Threat Intelligence, and more.
What is the Vulnerability Management Cycle?
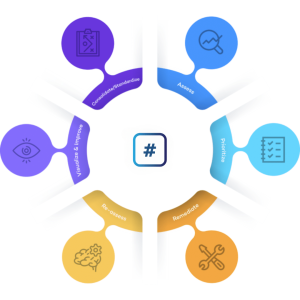
After gaining an understanding of what vulnerability management is, you might wonder about its lifecycle and process. The Vulnerability Management Cycle is a framework that provides guidance on the steps required to remediate security flaws within an organization’s network.
The vulnerability lifecycle starts with the discovery of security issues and concludes with validating whether remediation has been successful, before repeating continuously.
We have summarised the complete process of the Vulnerability Management Cycle below.
- Discover: Identify vulnerabilities within your organization’s network by carrying out vulnerability assessments.
- Consolidate: Centralise your assessment results in one place. This could involve transferring results from PDFs to a standardized database.
- Assess: Analyse your vulnerabilities to establish their severity, the likelihood that they will be exploited, and what impact they could have on your organization.
- Prioritize: Assign severity scores to your assets in line with your analysis, and other factors such as resource availability.
- Remediate: Implement your remediation program to resolve vulnerabilities in line with your organization’s priorities.
- Re-assess: Verify whether your remediation efforts have been successful. Ultimately, your vulnerability management process should reduce the risk of your organization being compromised.
- Visualize and improve: Continuously improve your vulnerability management process; resolve any bottlenecks and ensure compliance with your organization’s service level agreements. For example, could you reduce your time-to-remediate (TTR)?
Why is Vulnerability Management Important?
Vulnerability management is an essential part of an organization’s IT security strategy. Without an effective vulnerability management program, an organization’s data, personnel, and reputation could be at risk.
Effective vulnerability management helps IT security teams ensure that critical issues are discovered, analysed, and remediated before they can be exploited. This ensures that teams can minimize their organization’s attack surface and reduce the chance of cyberattacks. You can read more on cyber attacks in our cyber security risk management post.
Vulnerability management also helps organizations allocate resources more effectively. Not all security vulnerabilities pose the same risk, and many may not even need to be remediated. A good vulnerability management program helps security teams assess and prioritize vulnerabilities most effectively, so organizations can ensure that resources are suitably allocated.
Another reason why vulnerability management is so important is that an organization’s threat landscape is ever-changing. The Vulnerability Management Lifecycle illustrates that vulnerability management should be a cyclical process so that IT security teams can continuously be aware of evolving threats.
Vulnerability Management Cycle Best Practices
Continuous
Between security assessments your organization could be at risk. Vulnerability management should be an ongoing process, as new vulnerabilities could emerge at any time, and pre-existing vulnerabilities could become more critical. Read more on Continuous Vulnerability Management.
Intelligence-led
Intelligence-driven vulnerability management enables IT security teams to gain context of their issues, prioritize most effectively, and accurately evaluate risk. A process for gathering and referencing relevant cyber threat intelligence should be integrated with an organization’s vulnerability management life cycle.
Streamlined
How to Optimize the Vulnerability Management Cycle
The Vulnerability Management Cycle relies on many moving parts seamlessly working together to be successful. Consider the following points to help optimize your vulnerability lifecycle.
Unify your data: Vulnerability management can inundate you with data. You may find yourself emailing back and forth with vendors or hunting through PDF reports to find the results you need, which can be incredibly time-consuming. A vulnerability management system that unifies your data will save you time, frustration, and put critical information at your fingertips.
Automate to reduce human error: Transferring your PDF reports to spreadsheets is not only time consuming; entering data manually can lead to mistakes. This could pose serious risks to your organization, particularly if a critical issue is missed. Automation tools can lighten the load and help ensure accuracy, giving you peace of mind and significantly increasing the speed of your vulnerability management life cycle.
Streamline collaboration: Collaboration is key to keeping your organization secure. Whether you remediate issues in-house or work with a third party, a vulnerability remediation collaboration tool can help accelerate remediation and boost efficiency from start to finish.
Prioritize issues effectively: Establish a clear and consistent system for prioritizing your security issues. This will ensure your team remediate the most important issues first, which is not only a more efficient use of your resources but crucial for keeping your organization safe.
Define your most important projects: How does your team know where to begin if critical vulnerabilities exist across multiple projects? Ensuring your team understand which assets to prioritise will enhance your security posture and align your vulnerability remediation process with your organization’s goals.
Next Generation Vulnerability Lifecycle Management System
The Rootshell Platform is a vendor-agnostic vulnerability management solution. It enables you to manage results from any type of IT security assessment, including penetration tests, giving you the unique advantage of analysing different assessment results alongside each other, in one standardized format.
The Rootshell Platform’s unique features help you accelerate every stage of the vulnerability management lifecycle and enhance efficiency from start to finish.
How The Rootshell Platform Helps You Optimize The Vulnerability Management Cycle
- Consolidate Your Supplier Assessment Data: Import any assessment result into Rootshell; store data from any penetration testing vendor or security service provider in one centralised hub.
- Integrate and Standardize Your Assessment Data: Generate a database for your results in one consistent format. No longer analyse assessment results in silos; view data from different threat assessments alongside each other.
- Contextualize and Prioritize Your Assessment Data: Receive real-time insights and gain greater context of your issues, helping you prioritize most effectively.
- Streamline Your Remediation Workflow: Make remediation faster and more efficient, with third-party integrations, collaboration tools, real-time updates from testers, and more.
- Track and Validate Your Remediation Results: Measure your remediation efforts against your service level agreements and track key metrics, such as your monthly remediation rate.
- Visualize and Analyse Technical Risk Across the Whole Organization: Gain a holistic view of your global threat landscape; effortlessly analyse your technical risk with insightful dashboards and automated reporting.
The Rootshell Platform is a vendor-agnostic vulnerability management solution. It enables you to manage results from any type of IT security assessment, including penetration tests, giving you the unique advantage of analysing different assessment results alongside each other, in one standardized format.
The Rootshell Platform’s unique features help you accelerate every stage of the vulnerability management lifecycle and enhance efficiency from start to finish.
Cyber Threat Intelligence For the Vulnerability Management Cycle

Rootshell’s industry-leading Daily Exploit Detection integrates with exploit databases to serve you automated, continuous alerts as soon as an exploit becomes available for an issue within your digital estate.
Further Rootshell Platform reading: Vulnerability Management Maturity Model