Today marks the release of Rootshell Platform v2.5, featuring the platform’s new, powerful Active Exploit Detection, as well as greater coverage for exploit alerts and enhanced collaboration for teams.
Introducing Active Exploit Detection
Rootshell Platform can now automatically identify issues that are being actively exploited by threat actors in the wild.
Rootshell integrates with multiple threat intelligence feeds to alert users as soon as an active exploit is detected for an open issue.
The dashboard shows users how many issues are affected at-a-glance, and users can learn more about the exploit straight from the platform.
It’s impossible for teams to resolve every issue within their estate, and as only 2-7% of vulnerabilities are actually exploited, many may never be fixed. Without the right context, it’s challenging for teams to identify which issues to focus on, particularly as CVSS scores tell a limited story.
Rootshell provides the context needed to cut through the noise of vulnerability data, pinpointing which issues are truly most vulnerable to you and empowering teams to implement the most effective prioritization possible.
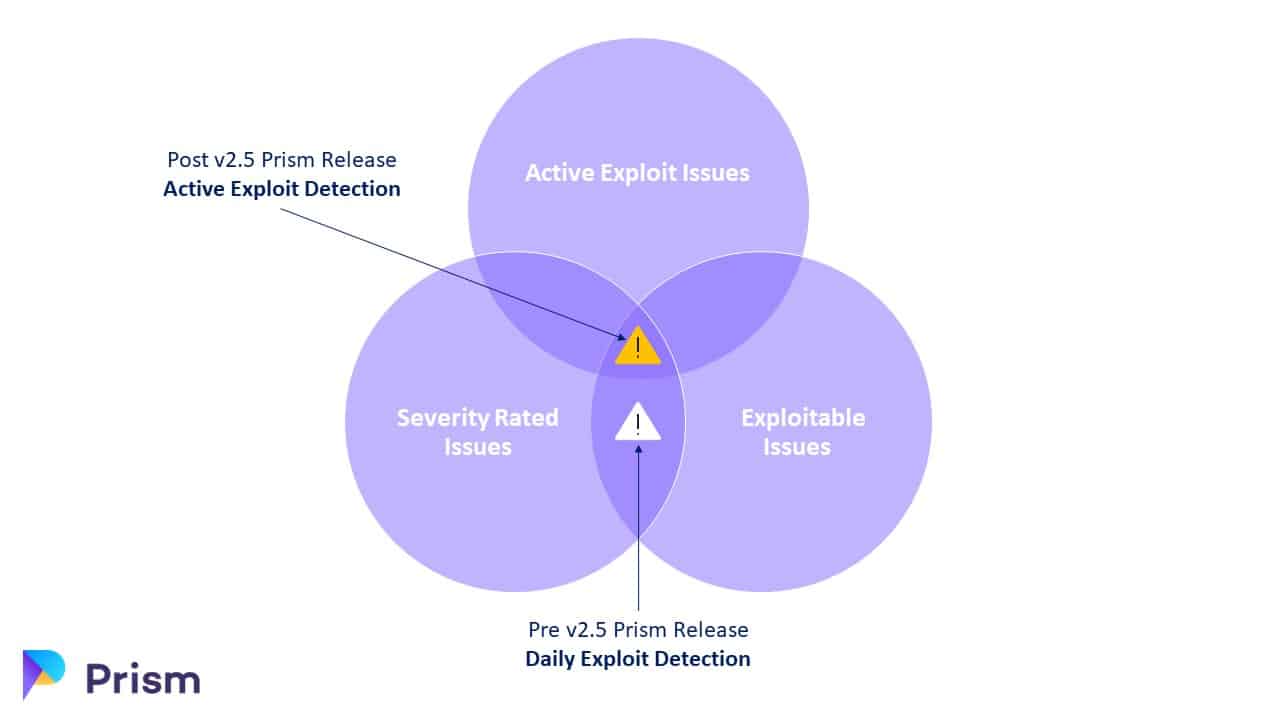
Together with Rootshell’s Daily Exploit Detection, which identifies exploits for vulnerabilities on a daily basis, Rootshell’s Active Exploit Detection overhauls point-in-time reporting and provides teams with powerful, continuous surveillance.
Greater Coverage for Threat Intelligence Alerts
Rootshell’s Daily Exploit Detection now integrates with The Cybersecurity and Infrastructure Security Agency (CISA), a US-based exploit resource.
CISA joins Prim’s integrations with Zero Day Initiative and Exploit DB to deliver even greater context for users.

Enhanced Collaboration for Teams
Rootshell users can now organize other users into teams. This enables Rootshell to more accurately reflect an organization’s structure and existing workflows, allowing users to delegate issues to the teams responsible for different parts of their digital estate.
Subscribe So You Never Miss an Update




